
.png)
Remote IoT Security
Simplifying IoT all on One Platform
Unboxed for You
Tosibox Platform is an automated, open cybersecurity platform for your operational technology networks and infrastructure. It scales from one user and one device to an enterprise-level OT network solution with hundreds or even thousands of users, devices, and sites connected. Tosibox Platform fits all industries and organizations, regardless of the size or vertical, and is designed to meet your needs today and well into the future.
Certified Cyber Security
Tosibox is ISO27001 certified, underlining the importance we place on protecting customers´ data. Their platform security is based on automated firewall settings and point-to-point VPN technology with 256 Bit AES data encryption. Tosibox Platform supports Layer 2 and layer 3 routing functions and protocols.
100% Fully Automated
Our patented automation helps eliminate human error saving time and money while building, maintaining, and expanding your OT network environment. Our patented technology ensures the highest security and instant connectivity with no 3rd party cloud routing or static IP addresses needed.
You Own the Data
A healthy building network can lower operational costs and conserve energy; all while self-managing to minimize maintenance time as the network grows.
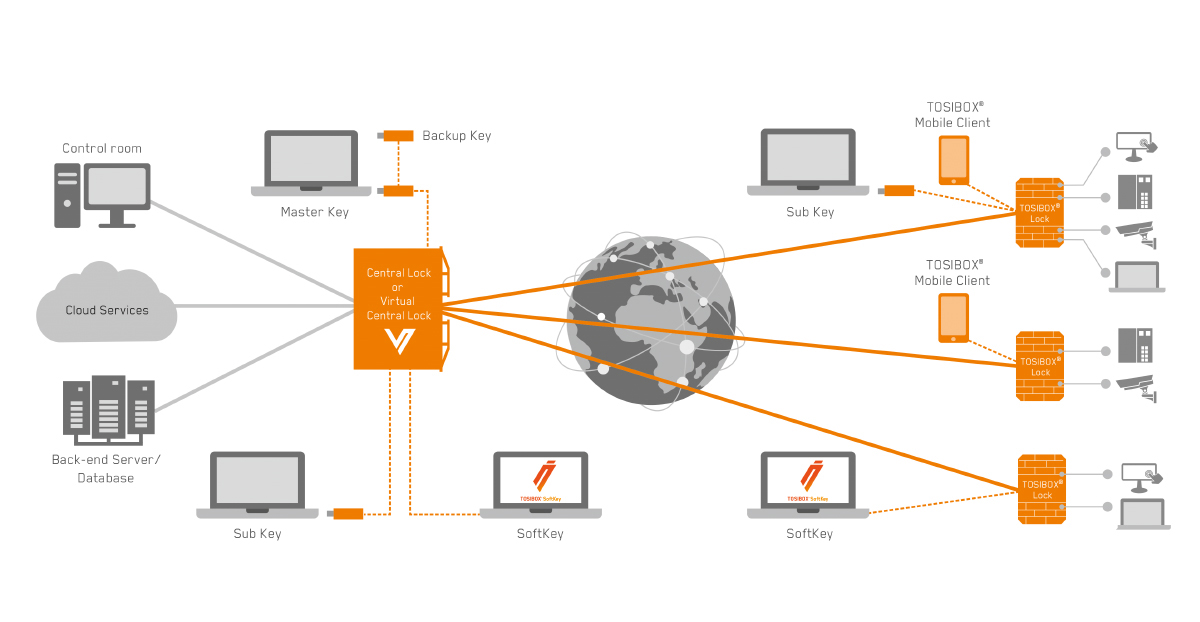
How it Works
With TOSIBOX® you can create a fully secure remote connection within minutes, and without special IT skills. You can build and manage networks and IoT infrastructures with the easily expandable and timeless solution.
We offer centralized real-time management of your devices and access control that help you generate cost savings. With TOSIBOX® adding new devices or users into the network is simply drag and drop, whereas with old-fashioned IT networks completing the same task takes days or weeks.
Build your IoT Ecosystem with Tosibox®
Modular TOSIBOX® Technology
With modular TOSIBOX® technology, you can build and manage a secure IoT infrastructure in minutes. The TOSIBOX® IoT ecosystem can be tailored according to your needs.
TOSIBOX® solution creates a direct VPN tunnel between TOSIBOX® Lock and Key. The solution consists of modular components that offer unlimited expandability and flexibility. All products are compatible with each other as well as internet connection, operator, and device agnostic. The system works both in internal and external networks.
Let us help you get secure remote access today!
Let Stromquist Assist you in getting started today!
The Technology


TOSIBOX® Key
Is a client used to access the network. In addition to a Master Key, the ecosystem can have several users with more physical keys, mobile app or software licenses.
TOSIBOX® Lock
Is a router with firewall sharing access to devices. One TOSIBOX® Lock protects all devices behind it. As the company grows, more Locks can be added to various locations.
TOSIBOX® Virtual Central Lock
Is the platform for easy network and access rights management. You can limit access, add new users and objects simply by drag and drop.
TOSIBOX® Locks
TOSIBOX® Locks 200/500 are an intelligent remote access and networking device that serves as an endpoint for secure remote connections. Devices connected to the Lock are securely accessed over the Internet and most LAN and WAN networks through an encrypted VPN connection.
NAT and firewall friendly, the Lock's patented Plug & GO connection method takes you out of the box and into use in less than 5 minutes, without the need for software installations, network configurations or special skills.


TOSIBOX® Keys
TOSIBOX® Keys are an intelligent cryptoprocessing device that enables a secure connection between your computer and one or more TOSIBOX® Locks, giving you full visibility and control over the network devices connected to the Lock.
Connections are established through a secure, encrypted VPN tunnel over the Internet or other common WANs and LANs, and permissions can be easily granted, revoked, and configured in an unlimited number of ways.
TOSIBOX® Softkey
SoftKey is a computer software that enables a secure connection between your computer and one or more TOSIBOX® Nodes, giving you full visibility and control over the network devices connected to the Node.
The SoftKey works without a physical TOSIBOX® Key device. The SoftKey corresponds a Sub Key that is controlled via a physical Master Key, and therefore it cannot be used to create more keys or Mobile Clients. The access rights are granted and controlled from the physical TOSIBOX® Key, after which the SoftKey remains bound to it. The access rights are device-specific and non-transferrable.
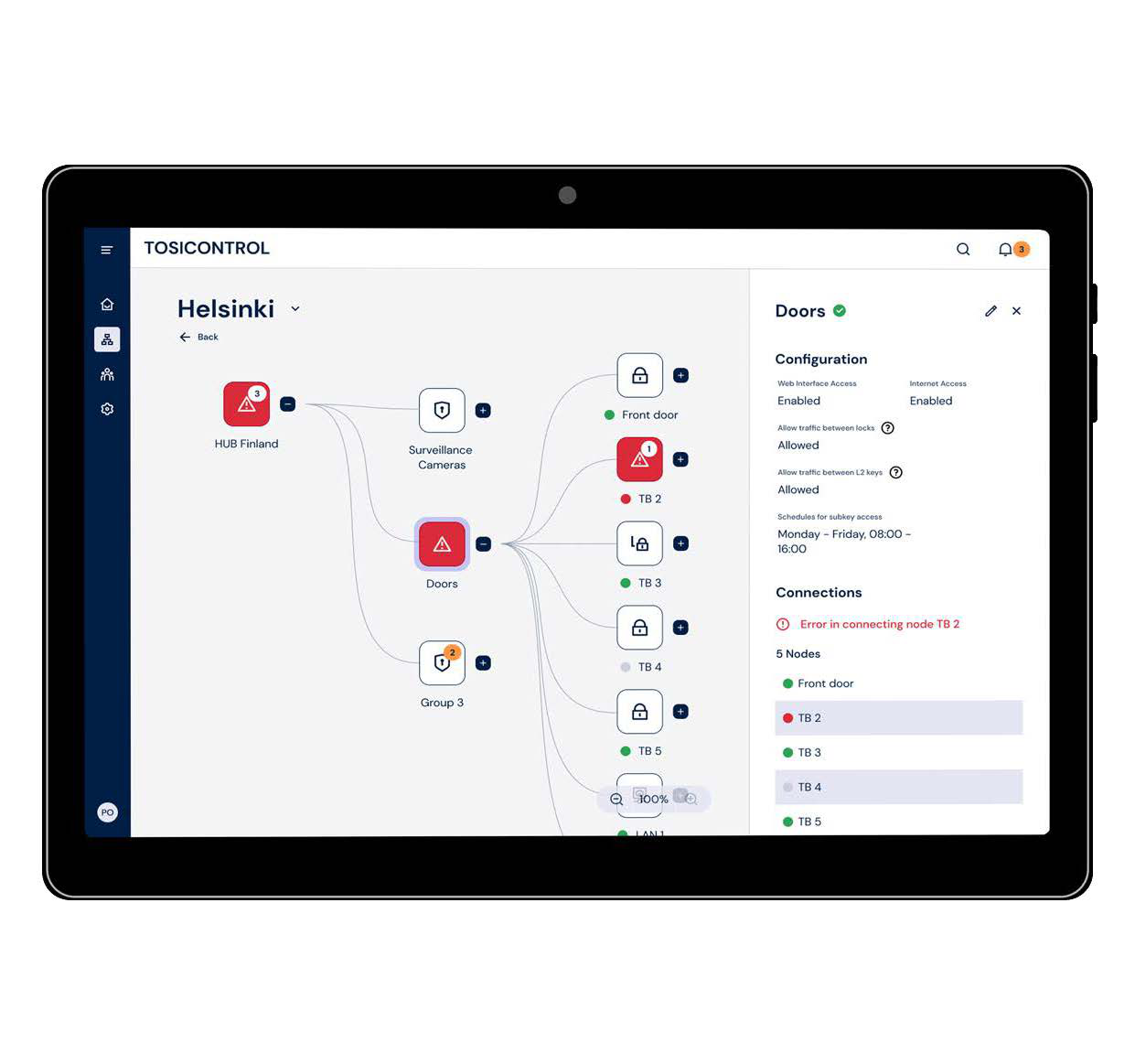
TOSIBOX® Hub (Virtual Central Lock)
The Tosibox Hub is the platform for OT network and access management. You can limit access and add new users and objects simply by drag and drop.TOSIBOX® Hub cuts access management work time from days into minutes, enabling easy management of big networks without the need for complicated network configurations.
TOSIBOX® Hub turns your Tosibox ecosystem into a controlled OT network of always-on VPN connections for remote maintenance, continuous monitoring, real-time data collection and data logging.
Because it’s virtual, it can be deployed in your office network, in leading cloud services AWS or Azure, or anywhere else where you prefer.
TOSIBOX® Virtual Central Lock turns your TOSIBOX® ecosystem into a controlled network of always-on VPN connections for remote maintenance, continuous monitoring, real-time data collection and data logging
ACCESS GROUPS
- You can create access groups and add relevant members (Keys, Nodes , IP addresses, network ranges or MAC addresses) by drag and drop
- Members of the same access group can communicate freely, and members can belong to several access groups
VIRTUAL LAN
- HUB supports Virtual LANs enabling adding workstations or servers from one or more networks connected to the HUB LAN into an access group
- You may have different networks defined per customer, or you may want to separate your office network from production network, and arrange remote access to these networks differently
PROPERTIES
- With virtual platforms, it is possible to achieve a very high level of redundancy and fault-tolerance where failover time is measured in seconds
- Because it’s virtual, it can be deployed in your office network, in leading cloud services AWS or Azure, or anywhere else where you prefer
- Supports up to thousands concurrent VPN connections from Keys, Nodes or Mobile Clients
| Functions | Tosibox Hub |
|---|---|
| TOSIBOX® Plug & Go™ Technology | Yes |
| Mounting Options | N/A |
| Power Input | N/A |
| 3G/4G USB Modem Support | N/A |
| WAN Port | One required, dependent on virtual platform |
| LAN Port | One required, dependent on virtual platform |
| VPN Throughput | Dependent on virtual platform |
| VPN Connection Encryption | Blowfish 128 bit CBC, AES 128/192/256 bit CBC |
| VPN connection authentication | PKI, 3072 bit RSA |
| Concurrent VPN connections/td> | Dependent on virtual platform and license |
| Supported Platforms | VMWare ESXi, Microsoft, Hyper-V, Linux KVM |
| WLAN | N/A |
| Operating Temperature | N/A |
| Measurements | N/A |
| Power Consumption | N/A |
| Approvals | N/A |
| Product Codes | TBPLTFRM TBPLTCONN Required Connection Package |
The Tosibox key is a client used to access the network. The network can have several admins and numerous users using physical Tosibox keys, Tosibox Mobile Client App, or a Tosibox Softkey software license.
| Functions | TOSIBOX® Key | TOSIBOX® SoftKey | TOSIBOX® Mobile Client |
| TOSIBOX® Plug & Go™ Technology | Yes | Yes | Yes |
| Key Role | Master Key, Backup Key, Sub Key | Sub Key | Sub Key |
| Cryptographic key size and type | 2048 bit RSA, hardware-based | 4096 bit RSA | 2048 bit RSA |
| Data Encryption | TLS, Blowfish-128-CBC, AES-128-CBC, AES-256-CBC | TLS, Blowfish-128-CBC, AES-128-CBC, AES-256-CBC | TLS, Blowfish-128-CBC, AES-128-CBC, AES-256-CBC |
| VPN connection type | Layer 2 / Layer 3 (OpenVPN) | Layer 2 / Layer 3 (OpenVPN) | Layer 3 (OpenVPN on Android, IPsec/IKEv2 on iOS) |
| Mobile Client for Android and iOS | Yes (1 license incl.) | No | N/A |
| Two-factor authentication | Yes | Yes | Yes |
| Part # | TBK2 | TBSKL1, TBSKL5, TBSKL10 | TBMC1, TBMC5, TBMC10 |

